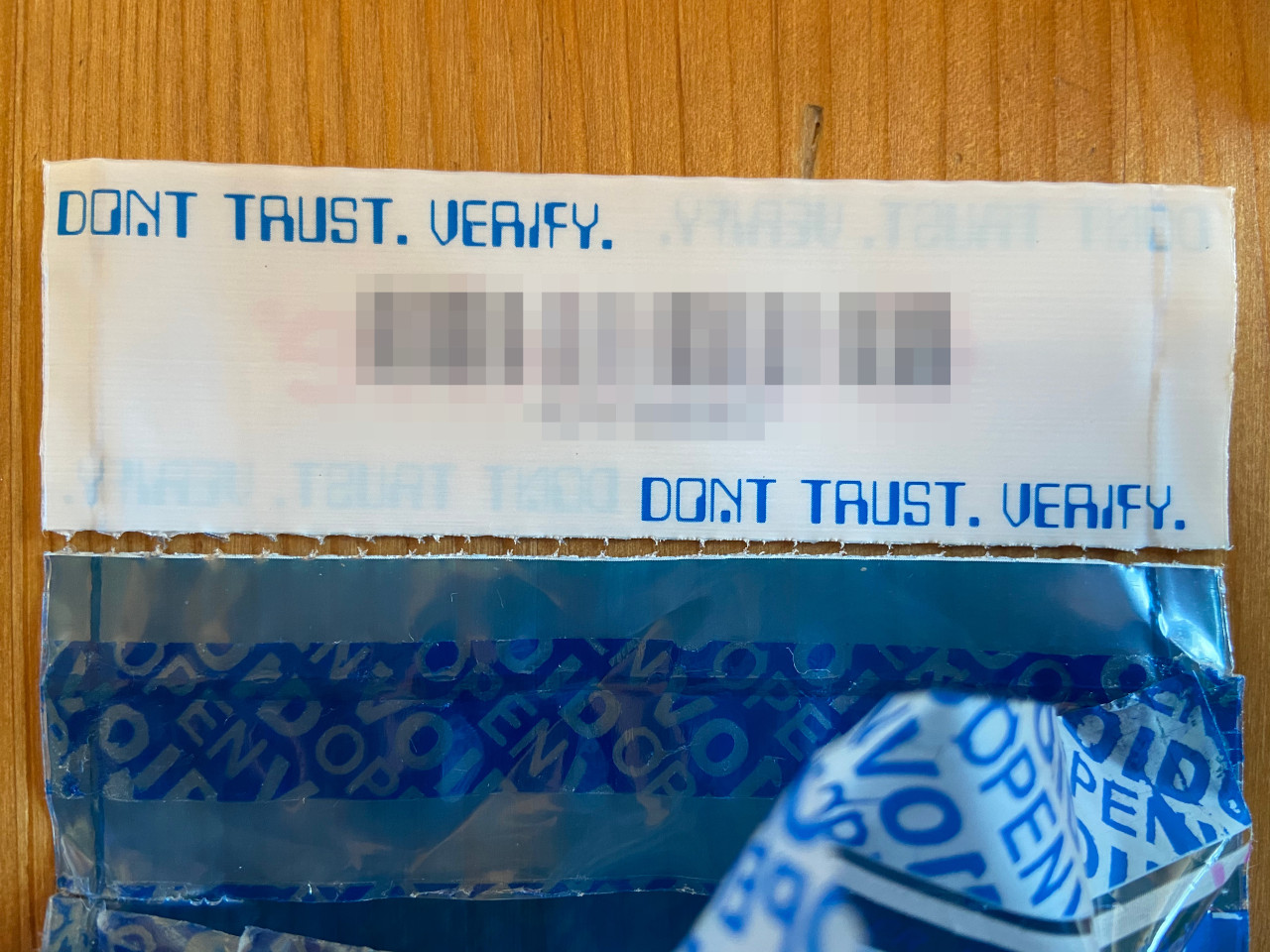
Checking for supplychain attacks on hardware wallets
The recent raise in Bitcoin prices inspired this article where we purchased a hardware wallet and reviewed all the steps to ensure a safe delivery and then checking for possible tamperings. We will go through the tools made available by Coldcard to inspect the packaging.

While ordering your hardware wallet you should deliver it to a mailbox address which reduces practical risks that have been lately in the spotlight due to an hack into the customers database of one of the major wallet producers. Other practical recommendations would be to use burner phones and single use emails, the phone and email are relevant only for Customs Clearance, in fact Customs may ask additional information like tax id or other details. Once the package is arrived though there is no longer the need to use such email and phone number. Finally, in the case of Coldcard you can require them to destroy all of your data, when you do so they warn that every information which was on the shipping label has been seen by various other parties, so that's why using a mailbox is very important.
Before opening the package you'll need to check the borders, in praticular close to where the plastic has been melted to close the envelope. A clean way to open the package would in fact be to cut along the molding line, extract the wallet, tamper with it, put it back and melt the plastic again. In practice the melting line should be about 1mm in width with a small geometric pattern repeating. If the melting line is larger or clearly loses the pattern, then something is strange about it. The dimension of the package should also be checked: there should be a clear blue border and the melting line should be near it or over it. If someone naive would cut the bag entirely on the side and then close it, it would be quite easy to spot the missing blue border.
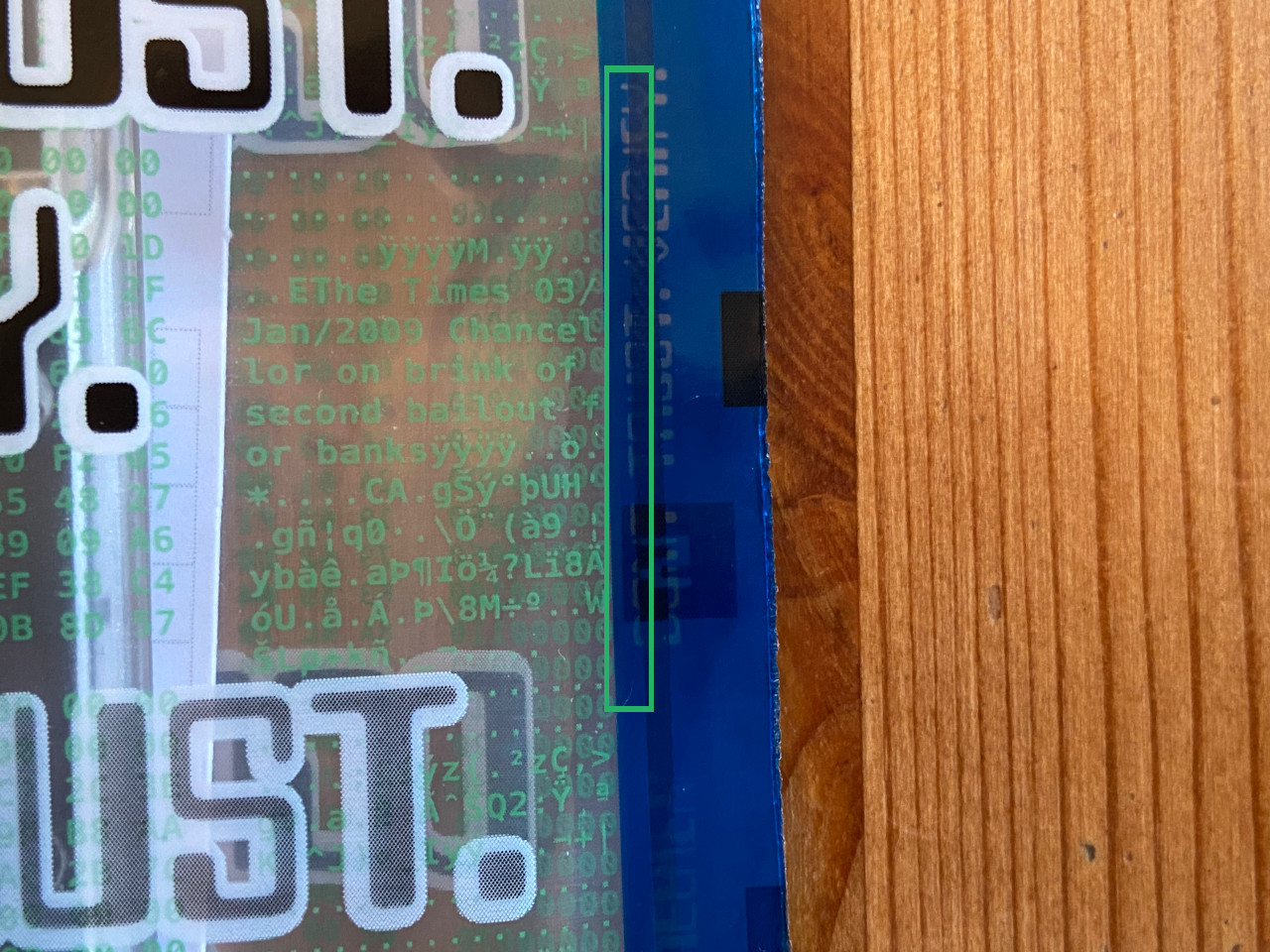
On the package and inside of it there's a packaging number which is also imprinted in the memory of your coldcard. This is only helping you to determine if the wallet is in the expected bag, the bag itself can be completely copied so also that number would be copied. There is no way for the receiver to determine if the bag itself is authentic but this is not something that can be solved with plastic bags. The tools offered are a nice effort but the important part is to hide in the mass and make it difficult, for external observers, to estimate how the coldcard will be used.
Once the bag is open, you'll find inside a tag which was the top part of the plastic piece from which the packaging was built. You can double check that the tag is indeed coming from that bag by looking at the cutting points and checking the width of the tag against the bag. Another thing to control is that the melting lines are the same and continue on the lower part of the bag.
Finally the coldcard is fired up and it shows the package number flashed in its memory. When choosing a way to store bitcoin the first step is to determine whehter your machine is more likely to be corrupted or the company seeling the hardware is impacted by a malicious supply chain. The i) reputation of the hardware company and ii) whether it's possible to review what software is installed on the hardware, are major decision drivers. In general devices that are often connected to the internet and used for day to day activities should be considered corrupted (or corruptible if identified). Once this assessment is done one can decide how to procede.
Coldcard has a lot of interesting functions for a developer: like handling partially signed transactions and having a completely open source approach, so for educational purposes it is definitely a good purchase. On the other hand for "top tier" security we discourage using single point of failure approaches, so coldcards can be part of a broader setup.


